Boost efficiency with AI-powered automation that integrates seamlessly into your workflow—no disruptions, just smarter operations. Learn how AI works quietly for you.
Boost efficiency with AI-powered automation that integrates seamlessly into your workflow—no disruptions, just smarter operations. Learn how AI works quietly for you.

Learn how to spot and avoid scams after natural disasters. Protect your donations and ensure they help those in need with these essential tips.

Upgrading to Windows 11 strengthens business security with advanced features like zero-trust architecture and hardware-based protection.

Discover how customizing off-the-shelf software can save costs and boost efficiency for growing businesses. Fully custom options also available.

As we head into 2025, it’s time to focus on strengthening your business’s defenses against ever-evolving cyber threats. Start the year off right by committing to these top five cybersecurity resolutions that will protect your business and your bottom line.

Windows 10 support ends Oct. 14, 2025. Upgrade to Windows 11 for security updates, better features, and enhanced performance. Learn how to prepare today.

Stay safe this Halloween with 6 spooky cybersecurity tips! Protect your business from phishing tricks, haunted links, and lurking cyber threats.

The Enemy Within The enemy is sometimes from within. When most organizations think of cybersecurity threats, they think of external criminals but never an internal employee. In an article from earlier this year linked here, we learn about a case out of Singapore where a disgruntled employee deleted all 180 test servers after he was […]

Back-to-school photos are fun to share, but be mindful to protect your child’s privacy. Follow these simple tips to stay safe on social media.
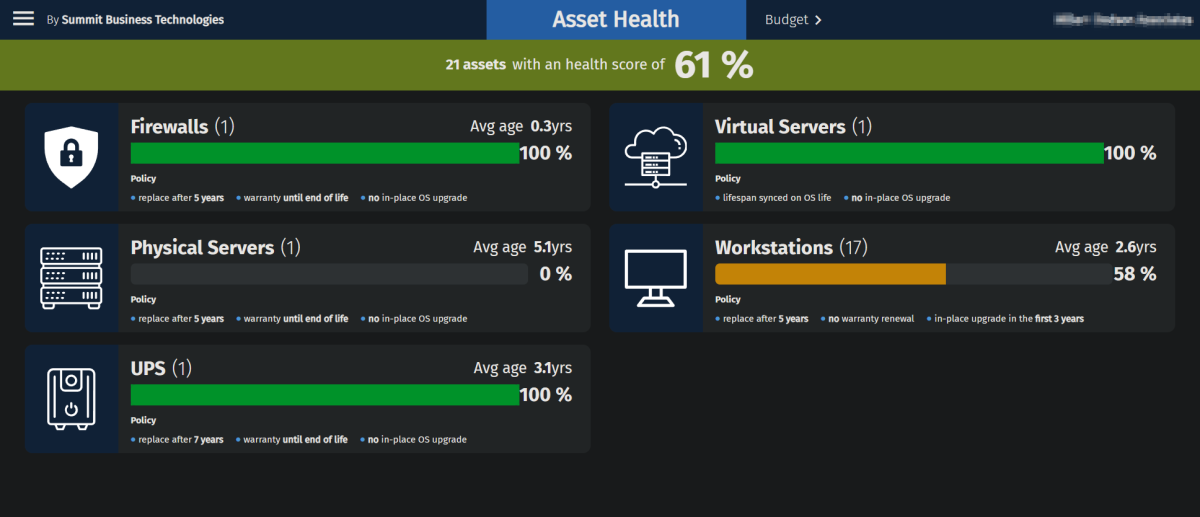
At Summit, we believe in the power of regular Technology Reviews to keep your IT systems running smoothly and your business thriving. Here’s how these periodic reviews can benefit you: A Clear Picture of Your IT Status Technology Reviews give us a chance to assess the current state of your IT systems. […]