If Q4 isn’t stressful enough for organizations, cyber criminals will make sure it is. The near constant occurrence of cyberattacks ramps up even more in advance of Halloween and the holiday shopping spree.
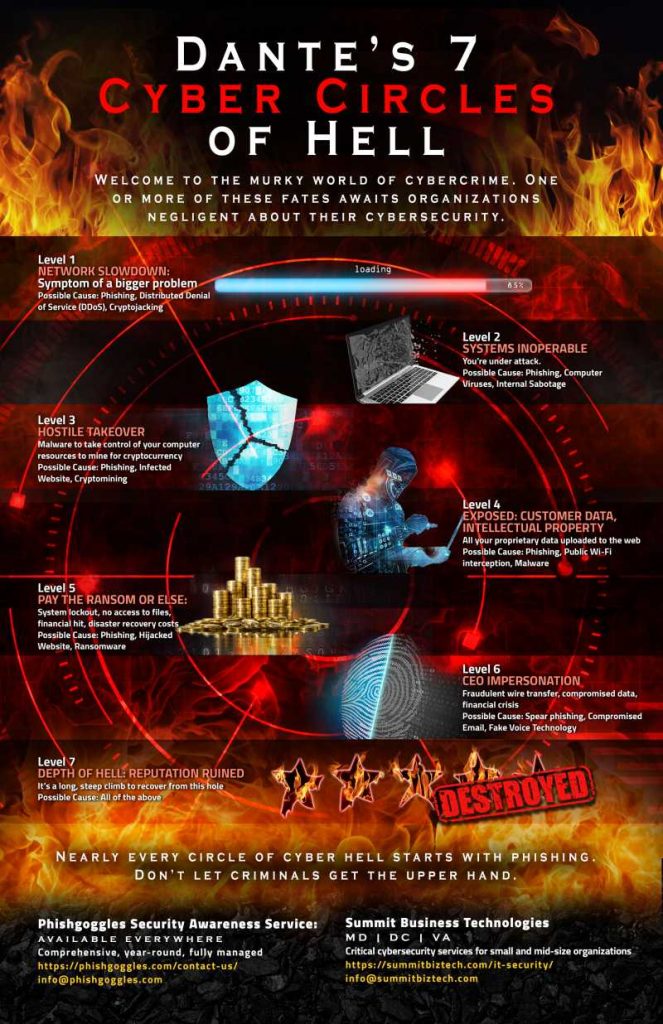
If you have done little to train your staff to identify cyber threats or convinced yourself that anti-virus/malware applications are sufficient deterrents, you have a starring role awaiting you in Dante’s Cyber Infernor.
This chart says it all.* It shows how cyberactivity climbed in Q4 2018, as hackers pulled out the stops to take advantage of Q4 tax filings, end of year financials, holiday shopping and distracted employees. For them, today kicked off the most wonderful time of the year.
For organizations, the 7 Circles of Hell include network slowdowns, inoperable systems, computer takeovers, exposed data, system lockouts, CEO impersonations and ultimately, reputations ruined. It’s a long, steep climb to recover from this descent.
Nearly every circle of cyber hell starts with phishing.
A recent report found that 95 percent of cybersecurity breaches are due to human error. 95 percent. And 4 in 10 cyberattacks target small businesses. Non-secure user names and passwords give hackers a better chance of success.
Hackers know that your people are your weakest link, unless you have immersed them in year-round security awareness training.
The rate of attacks is nearly constant. According to a University of Maryland study, computers with internet access are breached every 39 seconds, on average. That works out to 4 million records stolen from breaches every day, more than 158,000 per hour, 2,645 per minute and 44 per second. Those numbers according to Cybersecurity Ventures.
Don't let cyber criminals get the upper hand.
Ginni Rometty, IBM chairman, president and CEO, was recently quoted as saying, “Cybercrime is the greatest threat to every company in the world.” She’s right.
Take a minute to look at Phishgoggles.com. It’s a year-round, fully-managed security awareness service that has reduced employee response to phishing up to 75%. Phishing, awareness training, participation tracking, performance reporting—all done for you. It may be the most cost-effective decision you make this quarter.
For a visual depiction of Dante’s Cyber Circles of Hell, request our poster – and hang it where your employees can see it.
*Proofpoint: 2018 Malware by Quarter